Every year we witness an increasing number of cyberincidents affecting industrial facilities and critical infrastructure objects. Sometimes, these unfortunate events result in significant financial losses. In May 2016, for example, ransomware attacked the power and water utility at Lansing, Michigan, resulting in a loss of about $2 million. This incident didn’t affect the industrial network, but other attacks damaged industrial processes. For example, the attack on the systems of Prikarpatyeoblenergo carried out by the BlackEnergy APT group in late 2015 left tens of thousands of Ukrainians without electricity. Moreover, industrial incidents are getting more public and resonant, such as recent geopolitical speculations including the Burlington Electric hack story or Turkish officials’ claims about a cyberattack of US origin on its national power grid.
As a result, many industrial companies, as well as vendors of ICS (industrial control systems), are now alert to the issue and are devising ways of avoiding such threats and minimizing potential impact. Unfortunately, their efforts are currently misaligned, with each of the stakeholders trying to implement a separate cybersecurity strategy, ultimately making it harder to build a truly efficient cybersecurity framework. Moreover, because of the immaturity of the market, it’s the rare ICS cybersecurity specialist who is able to identify adequate cybersecurity measures for a specific facility. Beyond that, to properly secure an industrial object, one needs to be aware of constant changes on the threat landscape, adapting and improving the proper security system accordingly.
The market of cybersecurity solutions for industrial objects is on the rise, and an increasing number of players find it attractive. In 2016, Gartner analysts assessed the market and named more than 40 companies operating in this segment — although there are even more than that. In early 2015, half of them were unheard of. Today, all kinds of players — renowned security vendors, industrial automation vendors, start-ups, and even adjacent information security market players — are actively exploring the new market segment. In many cases, their approach is focused on network monitoring and/or finding anomalies in technical processes. But how do we know which methods and technologies are indeed optimal as a basis of cybersecurity practices for industrial objects?
Adaptive Security Architecture
We at Kaspersky Lab consider the Adaptive Security Architecture (ASA) by Gartner the most efficient model to build up cybersecurity practices for industrial objects. Initially, it was designed as a framework for solutions against targeted attacks rather than for security at industrial facilities. However, ASA is universal and now widely used as a complete security model reference for enterprises. It encompasses four types of action regarding a potential cybersecurity incident stage: Prevent, Detect, Respond, and Predict.
This model’s unique feature is an ability to proactively respond to a threat and protect a technical process from any kind of incident. That includes targeted attacks, the usual malware infections, software and hardware errors, and even human factors. The maturity of a company’s cybersecurity function is based on how it delivers on each of the ASA stages. But simply copying ASA, which was initially designed for traditional corporate cybersecurity, won’t help to effectively protect an industrial object. When using the framework in real-life conditions at the object, one should consider operational technology (OT) domain specifics, all technical peculiarities of the process, and human factors.
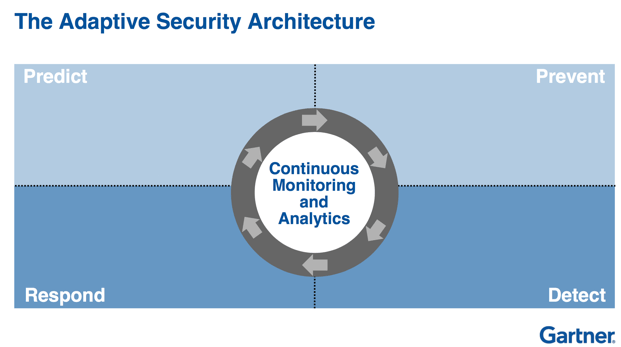
Usually, ASA is explained and implemented with the Prevent stage; it’s the most obvious choice. In that case the implementation should end with the Prediction capability (see the scheme above). For any kind of environment, we consider Prediction the pillar and the most important part of a truly efficient cybersecurity framework, and so we start the interpretation of the ASA model for industrial objects with this stage.
Predict
The Predict segment defines how good an organization is at predicting attack vectors, and it also involves taking into consideration the specifics of the industry. This capability ultimately helps to proactively address cyberattacks. Within today’s model of mature enterprise cybersecurity, the Predict stage is based mostly on threat intelligence. As a rule, mature companies with well-designed cybersecurity practices have security operations centers. Those centers rely on numerous sources and are able to get real-time threat intelligence from professional suppliers such as Kaspersky Lab. However, to make real use of threat intelligence, a company needs its own threat response center and a professional team of security experts able to predict incidents based on incoming data, as well as to reconfigure networks and to design their own security systems and strategies.
Such departments have been common in large enterprises for quite a while now, whereas at industrial objects this painstaking job is typically handled by a few specialists. In most cases, these specialists do not even belong to the same department, making threat intelligence of little use to them; they simply wouldn’t be able to leverage the information. At the same time, that does not mean the Predict stage cannot be implemented for industrial objects.
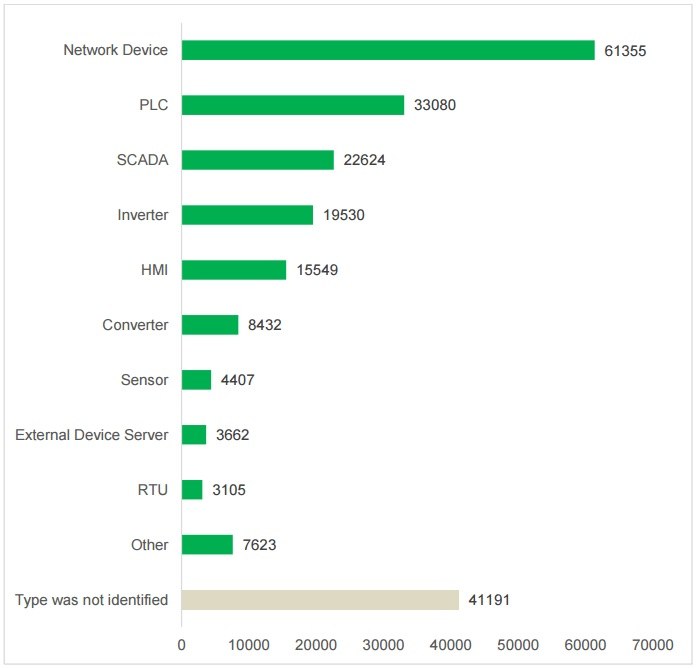
If this setting perfectly describes your industrial object’s modus operandi, the most sensible course is to defer specialized industrial threat intelligence feeds (some market players declare they are ready to provide such data to industrial objects) for the future and start with open data analysis. For example, you might make use of public threat intelligence sources about availability and vulnerabilities of industrial infrastructure (Shodan, Censys, and Vulners are just a few examples of specialized search engines). By the way, we used Shodan, among other tools, to conduct our own research, which found that a huge number of ICS components all over the globe are easily accessible online and can be compromised through one of the numerous vulnerabilities that typically plague them. So, we would recommend starting by checking the accessibility of your assets via publicly available tools, either on your own or with the help of industrial cybersecurity experts. If you do that proactively, you’ll have a chance to reconfigure your systems before somebody else finds your vulnerabilities — it’s a good Predict move.
One of the critical measures you might undertake at the Predict stage is an industrial cyberincident exchange among organizations operating within the same industry. It makes perfect sense: Adversaries who find success attacking one organization are likely to try reusing methods to hit a similar target. So, the experience of one victim should be leveraged as part of a prevention strategy.
A lot of organizations already facilitate this type of information exchange all over the world. The United States leads in this domain, with ISACs (Information Sharing and Analysis Centers) active in almost all industrial segments, consulting market players on critical objects’ cybersecurity. In most cases, such consulting entities are state-related organizations, which also impose additional regulatory pressure on businesses. Such centers, besides fulfilling an important mission, are notorious for their tedious audits and requirements to report any single security incident in detail.
The problem might be solved by similar commercial organizations that are enabled to provide analysis of recent incidents to industrial organizations and can act under nondisclosure policies. Organizations of this kind already exist, and one of them is our very own Kaspersky Lab Industrial Control Systems Cyber Emergency Response Team (KL ICS CERT). It’s been around for a relatively short time but offers information exchange services to many industrial organizations all over the world.
Another element of the Predict capability is a security audit of industrial systems and specialized penetration tests by third-party experts. Quite a few companies provide such services, but one should choose experts carefully. Some companies dispatch traditional infosec experts to run security audits at industrial objects. Of course, these experts are professionals. They test your network perimeter and availability of Web services and may even find some vulnerabilities. However, the results of such audits do not necessarily reflect the true level of industrial object cybersecurity. That’s why our teams that run such audits include both cybersecurity experts and ICS engineers with years of experience. With such specialists engaged in one team, audits can be run efficiently in both IT and OT domains and yield adequate results. Besides, Kaspersky Lab offers training for third-party security experts, teaching tips for pentesting at industrial objects.
Also, to make Predict practices work, your cybersecurity personnel, regardless of how many they are, should be fully aware of the trends and news of the cybersecurity world. We offer courses that help to train ICS security professionals among managers, responsible for industrial cybersecurity.
Prevent
Prevention is the cornerstone capability in a traditional cybersecurity framework. But for industrial cybersecurity, it’s the most controversial one. When a threat infiltrates a traditional corporate IT infrastructure, blocking it is the best action to take. However, in industrial environments, rashly blocking even a genuine threat, let alone false positives, can cause significant losses if the affected technological process is taken down. This might have a number of consequences, including catastrophic outcomes, if we’re talking about critical infrastructure objects.
That’s why many industrial automation specialists judge traditional prevention technologies, including antiviruses, harshly. They have good reason, though: Traditional products are not built to take ICS specifics into consideration.
Proper industrial prevention solutions include purpose-built protection capabilities that are designed to prioritize process continuity and are integrated smoothly with SCADA systems and other ICS components. Compared to classic antivirus products, these solutions put into priority specialized application and device controls (which is logical; engineers tend to run different applications or use their own devices when working at objects) and network security technologies. However, antivirus technologies are still very important for industrial systems. For example, our Anti-Cryptor fights against ransomware, which becomes a real threat for industrial infrastructure. Also, unlike classic workstation security products, industrial security agents should operate months without reboot.
Some industrial automation technologies require special care. In addition to the aforementioned capabilities, our Kaspersky Industrial CyberSecurity for Nodes has some unique features, such as PLC Integrity Check, which ensures the integrity of programmable logic controllers. It prevents attacks that implant malicious logic into the controller, aiming to swap projects (remember Stuxnet?).
The other important point is that the entire security management model has been adopted as well. Now, Kaspersky Security Center can send security alerts to engineers, which means our solution provides data on security events directly to human–machine interfaces.
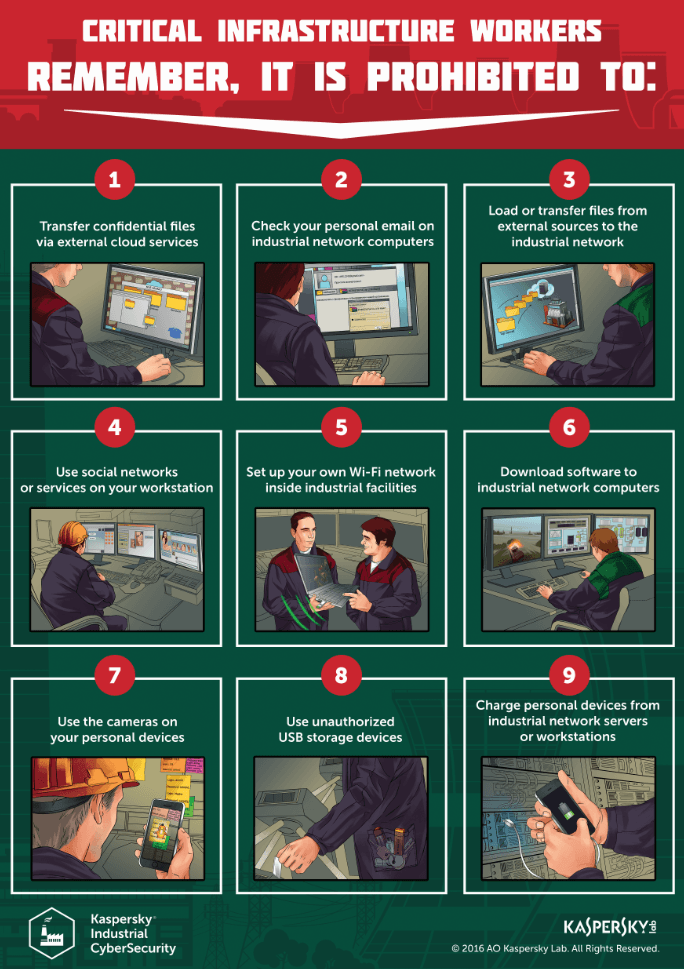
When deploying the Prevent capability, it’s crucial to raise awareness among personnel. According to research by the SANS Institute, the second most effective threat vector is unintentional security breach by facility staff.
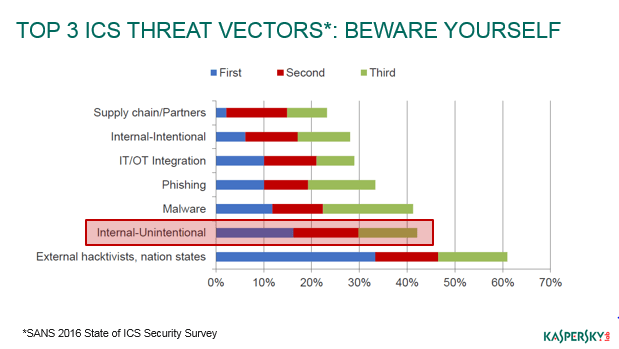
Engineers working at industrial sites tend to make all kinds of mistakes. For example, without any malicious intent, they connect their personal devices to a facility’s networks or roll out their own Wi-Fi networks within the secure perimeter. That is why basic cybersecurity awareness drills and training are critically important for all employees responsible for automation systems’ operations. Based on our experience, we can state that gamified trainings, such as the Kaspersky Interactive Protection Simulation, are the most effective way to boost awareness and raise prevention capability through it.
Detect
The Detect segment of the ASA framework is critical for industrial cybersecurity; in most cases, the Detect capability means passive monitoring without any interference with technological processes, which is crucial for those who make availability a top priority in the security process. Most current industrial cybersecurity market players offer network activity monitoring and traffic analysis. However, industrial solutions for detection are different from similar security solutions designed to protect against APT attacks.
Above all, specialized industrial solutions should be able to look inside automation protocols used to transfer process data (such as Modbus TCP, S7comm, IEC61850, and many others) and detect anomalies in such traffic. And network activity monitoring helps to detect new connections and run inventory checks within the entire industrial segment of the network, which is always a healthy security practice in an environment that suffers from a lack of transparency.
Such solutions have a key purpose: detecting targeted attacks that got past the technologies of the Prevent segment. There, the right technology helps to mitigate both external and internal threats. Consider a gas station employee responsible for daily operations, including fuel tanker filling. He wants to fit a bit more fuel into the tank, but the automation system won’t allow it. So he lowers the storage temperature via his control system, thereby “decreasing” the volume of the gasoline and squeezing a bit more into the reservoir. His reason is fraud — his accomplices then collect the extra volume during tanker stops and sell it illegitimately. In a conventional security system, this insider trick would have gone unnoticed, but a specialized industrial security monitoring tool would easily detect technological process discrepancies.
Finally, Detect solutions collect additional logs that facilitate digital forensics and incident response.
Respond
The final part of the ASA framework is Respond, which includes, obviously, threat response solutions. Of course, any infosec employee hopes not to have to resort to incident response systems, but in reality, it’s only a matter of time.
The key is here to be well-prepared for a potential incident and design a proper response plan. Obviously, a typical action routine won’t work here. Each industrial segment, or, in the best-case scenario, each industrial facility, needs to devise its own response plan — for example, as a vertically integrated oil and gas company, you can’t use IR plans for your midstream and downstream facilities because of huge difference in the operational technologies and technological processes. This plan should definitely be tested in the field (possibly through attack simulation).
It takes a lot of resources and efforts for a facility to investigate an incident on its own. Here, it makes better sense to approach specialized security services providers that can send their experts right away and take necessary actions on premise. However, very few companies offer this expertise specifically for industrial organizations. Kaspersky Lab has such a “parachute” team, but to be honest, even we feel the shortage of industrial cybersecurity professionals on the market.
The cybersecurity market’s common pain point is the lack of highly skilled professionals. And this shortage is even bigger in the industrial sphere, where a security expert has to be proficient in both information security and industrial control systems. That’s why in 2016 we began offering Digital Forensics in industrial environments among other training courses.
Another way to get help with digital forensics and incident response is to involve a local CERT, but ICS CERTs are still rare.
Also, let us repeat a tip from the Detect section: Using a specialized industrial security monitoring tool will facilitate forensics. In most cases, ICS/SCADA system logs are not enough to identify the attack vector and conduct thorough investigation.
Conclusion
Industrial cybersecurity is a very dynamic market, and every market player, including Kaspersky Lab, has room for improvement. As a provider of holistic industrial cybersecurity solutions, we understand that not all enterprises are ready to deploy the newest security technologies. There are a number of legitimate reasons for that, including short industrial maintenance windows and long update cycles, budget constraints, still-low awareness about existing industrial cybersecurity issues, and the necessity of proving the point to various decision-makers within an organization.
That’s why raising awareness about industrial cybersecurity practices among all employees comes first, way before the framework we describe in this article is implemented in real-life conditions. Doing so provides an extra layer of protection against social engineering attacks and facilitates migration to specialized solutions — people will understand the need for it. Let’s call it Step Zero.
However, the main thing to remember is that methods and solutions to fight all kinds of industrial cyberthreats are already available, and they will help with implementing the ASA framework step by step. For our part, we will continue developing this cybersecurity vertical as one of our priority directions — not only by evolving our Kaspersky Industrial CyberSecurity solution but also by expanding KL ICS CERT coverage, our global project created to help industrial automation vendors, industrial facility owner-operators, and security researchers coordinate their joint efforts to properly secure critical infrastructure objects.
 Industrial Cybersecurity
Industrial Cybersecurity

 Tips
Tips