Yesterday one of 2ch’s users attracted the attention of Russian media. This man streamed video from the hacked computers on YouTube. The anonymous user turned these sessions into a real online show. For example when a handful of victims approached their computers, he opened up a pornographic video in the browser right when they came close to their devices.

Hacking webcams is a popular activity for young hackers. While the general public has become aware of this creepy hobby only recently, it has actually been a “hobby” of hackers for years.
In 2014 a voyeuristic website popped up in the news. It streamed video from thousands of webcams located in 250 world countries. As it turned out, users all across the globe made the same simple mistake, which let the hackers in. The users kept the device’s default passwords or chose weak combinations like 12345.
Who is to blame for “hacked” private cameras? https://t.co/WItQAZKAbU #security #webcams pic.twitter.com/k7LcRXH6vX
— Kaspersky Lab (@kaspersky) November 21, 2014
The creepy website was closed but the problem did not go away. Last year users of the Russian humor site Pikabu started exploring the world through someone else’s webcam. A user posted a manual on hacking surveillance cameras and all hell broke loose. Readers studied the hacking 101 guide and went online looking for cameras with poor passwords, installed in WCs, flats and back-street brothels. And they succeeded!
So, massive webcam breaches happened from time to time. But in the most recent incident the scenario was completely different.
How could it happen?
2ch (or ‘Dvach’) is an anonymous website, popular among Internet trolls, moral and justice crusaders, people with ‘alternative’ sense of humor, young hackers — a variety of individuals actually, from all walks of life. Recently this website hit the headlines in relation to another scandal — 2ch users arranged a cyberbulling campaign against Russian porn actresses.
#Trolls expose #porn stars social networking accounts https://t.co/2mY8kh0JlJ #socialmedia pic.twitter.com/2tejy4TDZ9
— Kaspersky Lab (@kaspersky) April 22, 2016
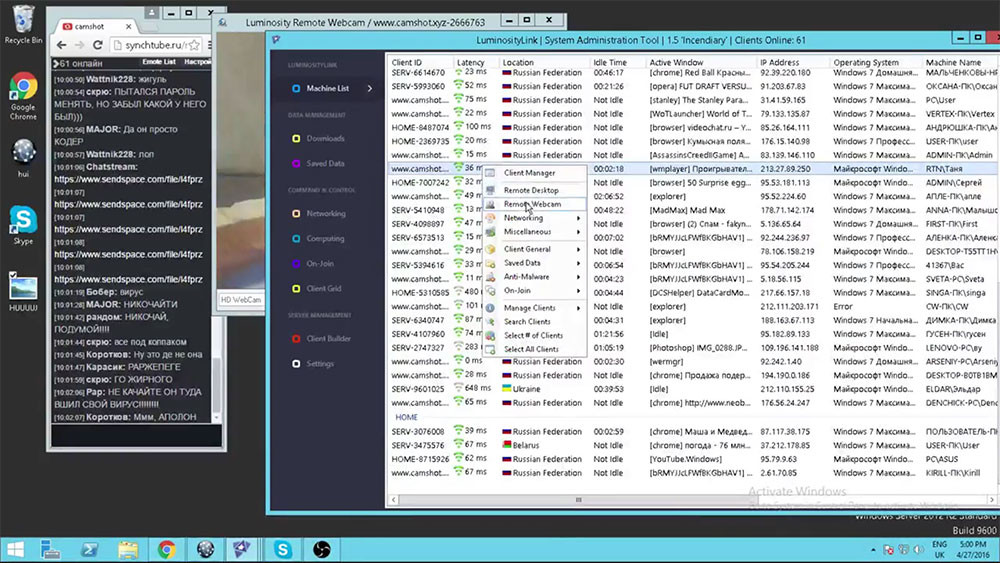
This time the public eye is focused on a thread of an anonymous user, who hacked computers of hundreds users in a variety of countries and streamed live video from them on YouTube. For several days (starting on April 26) 2ch users have been enjoying the possibility to spy on unsuspecting people, discuss their manners, appearance and room decorations.
The hacker has several tricks, which he uses to entertain viewers during the stream. The 2ch case is quite different from other incidents listed above: this time the hacker received almost full control over victims devices, not only their webcams. This lets him stage his streams creatively.
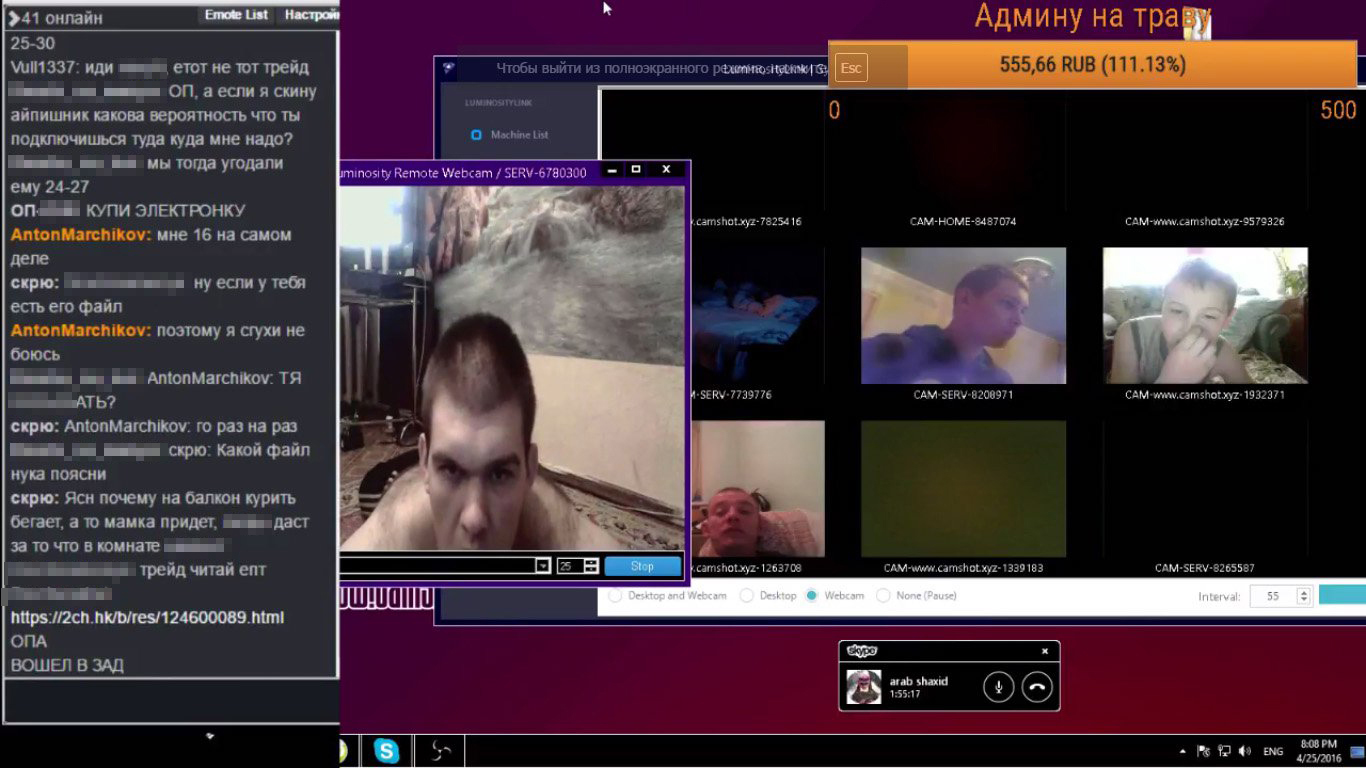
His favorite trick is to open a homosexual porn page when the unsuspecting user is near the computer, or show the victim’s VK.com page to the trolls. After this, the anonymous mass of trolls combine to cyberbully the hacked user on the social network.
During one of the sessions the hacker turned music on to wake up the PC owner. As TJournal reports, in most cases users don’t understand that their PCs are controlled by somebody else. “After seeing that something is wrong, many people turned on antiviruses or disconnected from the Internet. The hacker lost remote control over victims devices when Kaspersky solutions were launched” (quote from the article published on the TJournal website).
The first lesson is that you should NEVER, EVER turn off your security solution. If the people who were hacked *in this very case* did not turn it off, the hacker could not have invaded their computers in the first place.
How is it possible?
In this post we are talking about unusual hack: the criminal did not hacked webcams with unreliable passwords for his stream. Instead he compromised hundreds of PCs in several countries.
How did he do it?
In the thread he explained that victims downloaded cracks for computer games and other dubious software. For example, many users in the stream had some free video downloader called MediaGet installed. The hacker told 2ch users that 90% of such programs are delivered together with malware.
Having hacked these PCs with the help of malware, the criminal installed in compromised systems LuminosityLink — legal software, which is designed for computers remote administration. He used it to get full access to victims PCs, including their web-cameras and microphones.
Hacked Baby Monitor: Security Experts Warn 'Change Your Password' After Cameras Compromised http://t.co/MPHZd2Y5Bc via @HuffPostUKTech
— Kaspersky Lab (@kaspersky) April 28, 2014
Discussing the stream, 2ch users discovered that they can deceive even the owners of laptops with indicators, which light up when a software requests access to the camera. Hacking these devices is a tricky business, but it’s possible. The success depends on laptops model.
What can be done?
If you are not ready to become the star of yet another underground reality show, the easiest way to hide yourself from trolls is to tape your laptop’s camera. The thing is that this approach won’t protect you from the main threat: the hacked system would still be hacked and you wouldn’t even know about it.
Having access to your system, the culprit can steal data from your accounts (including your online banking), turn your PC into a part of botnet and use it to infect your friends’ devices. That’s why curtaining your laptop cam is not enough.
So which online habits should we change?
1. Downloading free software from third-party sites is risky. You would scarcely distinct a fake website from the legal one. So if you want to install software, you should download it from the developer’s website.
2. Many victims of the 2ch hacker turned their antiviruses off and tried to launch them again only when they suspected that something is wrong. If their security solution worked all the time and users followed its recommendations, most probably malware would be unable to reach their system. That’s why your antivirus should be active all the time.
3. If you don’t have any security solution at all, we highly recommend you install a decent one, like Kaspersky Internet Security. Among other useful features, it also protects web cameras from unauthorized access.
 privacy
privacy

 Tips
Tips