The goal of most attackers, regardless of how they go about their business, is to steal user data. That could be in small, discrete attacks on individual users or it could be in large-scale compromises of popular Web sites or financial databases. The methods may change, but the aim is the same. In most cases, attackers first try to get some sort of malware onto user machines, as that’s the shortest route between them and your data. But if that isn’t feasible for some reason, another popular method of compromise is the man-in-the-middle attack. As the name suggests, this attack vector involves the attacker placing himself–or his malicious tools–between the victim and a valuable resource, such as a banking Website or email account. These attacks can be highly effective and quite difficult to detect, especially for users who aren’t aware of the dangers the attacks present.
Man-in-the-Middle Attack Definition
The concept behind the MITM attack is remarkably simple, and it is not limited to the computer security or online worlds. In its simplest form, the attack requires only that the attacker place himself between two parties that are trying to communicate and that he be able to intercept the messages being sent and further have the ability to impersonate at least one of the parties. For example, in the offline world this could involve someone creating fake bills or invoices, placing them in a victim’s mailbox and then intercepting the checks that the victim attempts to mail back as payment. In the online world, the attacks are somewhat more complex, but the idea is the same. The attacker puts himself between the target and some resource that she is trying to reach. The attacker’s presence must remain unknown to both the victim and the legitimate resource he is impersonating in order for the attack to be successful.
MITM Attack Variants
The most common MITM attack involves an attacker using a WiFi router as the mechanism with which to intercept user communications. This can be done either by setting up a malicious router that appears to be legitimate, or by exploiting a flaw in the setup of a legitimate router in order to intercept users’ sessions on the router. In the former scenario, an attacker could configure his laptop or other wireless device to act as a WiFi hotspot and give it a name commonly used in a public area such as an airport or coffee shop. Then, as users connect to the “router” and attempt to reach sensitive sites such as online banking sites or commerce sites, the attacker can capture their credentials for later use. In the latter example, an attacker identifies a weakness in the configuration or encryption implementation of a legitimate WiFi router and then exploits that flaw in order to eavesdrop on communications between users and the router. This is the more difficult of the two scenarios, but can also be the more effective if the attacker is able to maintain persistent access to the compromised router for hours or days at a time. This gives him the ability to eavesdrop silently on sessions that the victims believe to be secure–say a session with a corporate email server–and gather large amounts of sensitive data.
A more recent variant of the MITM attack is what’s known as a man-in-the-browser attack. In this scenario, the attacker uses one of a number of possible methods in order to plant some malicious code on a victim’s machine that runs inside the browser. That malware then silently records the data sent between the browser and various target sites that the attacker has hardcoded into the malware. These have become more popular in recent years because the attack allows the attacker to target a larger group of victims and doesn’t require him to be in close proximity to the victim base.
Defenses
There are several effective defenses against MITM attacks, but nearly all of them are on the router/server side and give users no control of the security of the transaction. One such defense is the use of strong encryption between the client and the server. In this case the server can authenticate itself by presenting a digital certificate and then the client and the server can establish an encrypted channel through which to send sensitive data. But this relies on the server on the other end having such encryption enabled. On the other end, users can protect themselves against some kinds of MITM attacks by never connecting to open WiFi routers or by employing a browser plug-in such as HTTPS Everywhere or ForceTLS that always establishes a secure connection whenever the option is available. However, each of these defenses has limitations and there have been demonstrations of practical attacks such as SSLStrip or SSLSniff that can negate the security of SSL connections.
 data theft
data theft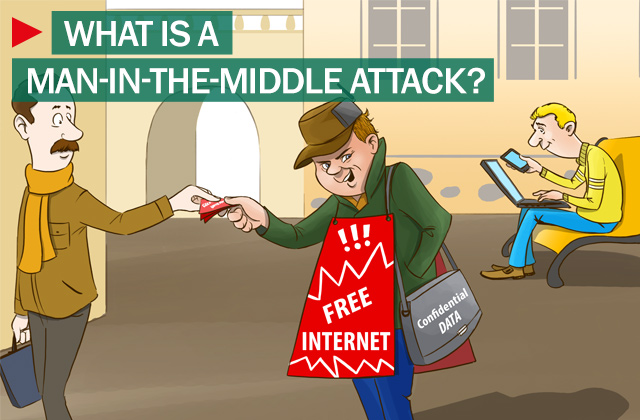

 Tips
Tips